I Built a GitHub Secret Leak Scanner After My Own API Key Was Exposed — What Happened Next Changed How I See Public Code Forever
It started with a mistake that cost attention.
My own credentials were exposed.
Not because of some advanced breach.
Not because of malware.
Just a simple developer mistake — a secret that should never have entered version control.
That moment changed how I looked at commits permanently.
Because once something enters public Git history, deletion is not protection anymore.
The history remains.
Forks remain.
Mirrors remain.
Anyone watching public events can see it before the owner even realizes what happened.
That was the exact reason I built my own secret leak scanner.
At first, the goal was personal:
Protect my own workflow. Detect leaks before they become damage.
But while building it, one thought became impossible to ignore:
If this can protect my own commits, then technically the same logic applies to every public repository being pushed right now.
So I expanded it.
I connected the script to GitHub public push events.
Pulled fresh commits.
Parsed only newly added lines.
Ignored noise.
Filtered hashes.
Matched known secret structures.
Measured entropy.
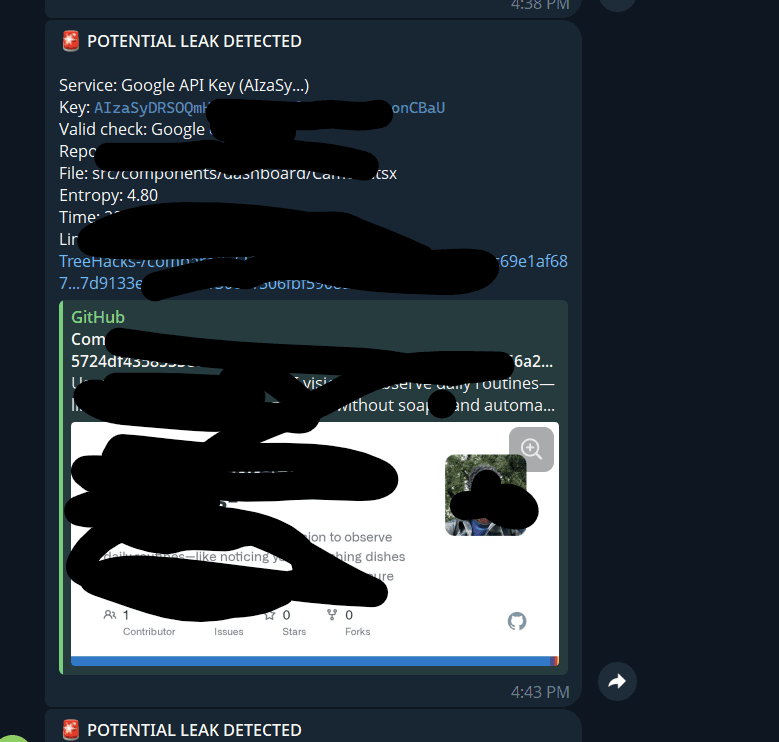
And pushed detections directly to Telegram in real time.
Then I left it running overnight on my local machine.
What came back was far beyond what I expected.
Overnight, More Than 30 Live Secrets Appeared
By morning, the script had collected more than 30 exposed credentials.
Not fake strings.
Not dead examples.
Live credentials inside public repositories.
Most were committed accidentally inside:
.envfilesconfig files
temporary test commits
forgotten debug code
The pattern was almost always the same:
A developer forgot one protection layer:
forgot
.gitignorepushed test code
committed environment values
assumed deletion later would fix it
But public commit streams move faster than cleanup.
The Most Disturbing Part: Many Keys Were Still Fully Active
Several exposed credentials were still valid when checked.
Different providers.
Different repositories.
Different owners.
And many still had available quota.
That is the moment where the real security question appears:
If one person running a local overnight script can discover this volume of exposed secrets, what happens when industrial-scale automated scanners are watching continuously?
Because they already are.
This is not hypothetical.
Public repositories are monitored continuously by bots, scanners, and automated systems.
The window between leak and exploitation is often measured in minutes.
Sometimes less.
One Repository Owner Changed Everything for Me
In one case, I contacted a repository owner directly.
I informed him that his credential was exposed publicly.
His first reaction was confusion.
Then concern.
Then one immediate question:
"How did you even find this?"
The answer was simple:
A script.
Nothing extraordinary.
No private access.
No exploit.
Just reading public push data.
He removed the repository history immediately.
That interaction changed my perspective.
Because what felt extraordinary at first was actually normal infrastructure in security ecosystems.
Then I Realized This Entire Category Already Exists Publicly
After digging deeper, I found many public projects already doing similar work:
secret scanners
commit monitors
token detectors
entropy-based leak finders
Some far more advanced than what I built.
Meaning this capability is not hidden.
It is openly available.
Widely known.
Already used.
That realization removed the illusion that this was unusual.
The real issue is not whether such scanners exist.
The real issue is how often developers still underestimate how fast public exposure happens.
Why I Finally Published My Own Version
Initially, I kept the tool private.
Because it felt sensitive.
But after seeing how many public scanners already exist, publishing became a documentation decision rather than secrecy.
The project is now public as:
Multi-API-Leaks-Finder
It monitors:
GitHub public push events
commit patches
added lines only
secret patterns
entropy signals
Telegram alerts
Supported detections currently include:
OpenAI keys
Anthropic keys
Google API keys
Groq keys
The Reality: Detection Systems Are Becoming Faster Than Developers Realize
At one point, I accidentally exposed one of my own test keys.
Within minutes, an automated alert arrived.
The provider had already detected the leak.
Revocation became immediate.
That confirmed something important:
The ecosystem is evolving fast.
Providers are watching.
Attackers are watching.
Automation is everywhere.
Which means developers must assume this:
The moment a secret becomes public, detection has already started.
Final Thought
The lesson was never that secret scanners are powerful.
The lesson is that public code is observed much more aggressively than most people imagine.
One accidental push can become someone else's free infrastructure.
And most leaks still happen through ordinary human behavior, not advanced failure.
That is exactly why secret hygiene must become default engineering behavior, not optional cleanup.
GitHub repository: